The web browser based management console allows for administration of the QUADStor VTL system. For Linux installations, if you have SELinux enabled on the system, ensure that you follow the instructions mentioned under "SELINUX CONSIDERATIONS" in http://www.quadstor.com/vtlsupport/145-installation-on-rhel-centos-sles-debian.html
Ensure that the httpd/apache2 server is running on the system.
In order to access the console, open a web browser and type the address of the QUADStor VTL system. Ensure that javascript is enabled in your browser. (Javascript is by default enabled for browsers)
Alternative the index html page can be accessed by http://<address>/vtindex.html
Once the HTML page loads you would be presented with a menu as shown in the following figure
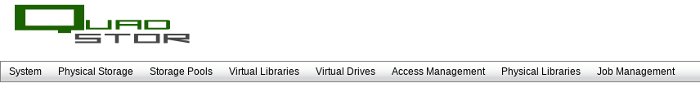
Each menu "System", "Physical Storage", "Storage Pools", "Virtual Libraries", "Virtual Drives", "Access Management", "Physical Libraries" and "Job Management" is a clickable link
Securing access to the web interface
With out any additional setup, the web interface can be accessed by any one from a browser. Access can be restricted and secured by simply two steps.
- http authentication using htaccess and htpasswd or with the new VTL authentication method
- SSL access
Setup is one-time only and is persistent across quadstor upgrades.
VTL Authentication
Starting with version 3.0.43 the VTL daemon can authenticate users accessing the web interface. Unauthorized users are redirected to a login page. To enable VTL authenctiation
Add the following to /quadstorvtl/etc/quadstor.conf. Create the file if it does not exist
EnableAuth=1
Run the following command to reload the configuration file
/quadstorvtl/bin/vtconfig --reload
Add a new user to access the web management interface. A new user can be added by
/quadstorvtl/bin/vtuser --add --user <user name> --password <passwd>
Or with short options
/quadstorvtl/bin/vtuser -a -u <username> --p <passwd>
Usernames and Passwords need to be a minimum of 8 characters can be up to 32 characters in length.
Usernames and passwords need to be ascii chars and can be _ or -
Read Only user
A read only user is a user with non administrator access. A read only
user can be created by
/quadstorvtl/bin/vtuser -a -u <username> --p <passwd> -r Or /quadstorvtl/bin/vtuser --add --user <user name> --password <passwd> --readonly
A logged in read only user can only view the VTL configuration, disk
configuration etc but cannot modify such as adding new users, new
disks etc. For now this user option may not be of much use
Listing users
/quadstorvtl/bin/vtuser --list Or /quadstorvtl/bin/vtuser -l
Deleting an user
/quadstorvtl/bin/vtuser -x -u <user name>
Log out
Closing the browser tab/window will automatically logout the user. Also a restart of the VTL daemon will logout all users. Log out button is work in progress
htaccess setup
Prior to 3.0.43 authentication could be enabled at the web server side. With VTL authentication this method is no longer required
1. In the cgi-bin directory create a file called .htaccess
2. Add the following lines to the file
AuthName "QUADStor VTL Authentication" AuthType Basic AuthUserFile /usr/local/www/apache22/cgi-bin/.htpasswd Require valid-user
Note that the "AuthUserFile" could be anywhere accessible by the web browser,but we chose the cgi-bin directory itself and the file needn't be named as .htpasswd
3. Create the .htpasswd file
htpasswd -s -b -c <htpasswd file> <username> <password>
For example
htpasswd -s -b -c /usr/local/www/apache22/cgi-bin/.htpasswd webadmin webadmin
4. Edit the httdp.conf and search for
<Directory ...cgi-bin> directory. For example on FreeBSD with apache22 it would be
<Directory "/usr/local/www/apache22/cgi-bin"> Options None Order allow,deny Allow from all </Directory>
Add the following line
AllowOverride AuthConfig Limit
For example the above configuration is now
<Directory "/usr/local/www/apache22/cgi-bin"> AllowOverride AuthConfig Limit Options None Order allow,deny Allow from all </Directory>
cgi-bin and httpd.conf paths
FreeBSD with apache22 /usr/local/www/apache22/cgi-bin /usr/local/etc/apache22/httpd.conf FreeBSD with apache1.x /usr/local/www/cgi-bin /usr/local/etc/apache/httpd.conf RHEL/CentOS 5.x/6.x /var/www/cgi-bin /etc/httpd/conf/httpd.conf Sles 11 /srv/www/cgi-bin /etc/httpd/conf/httpd.conf Debian Squeeze 6.x /usr/lib/cgi-bin /etc/httpd/conf/httpd.conf
Enabling SSL access
SSL access setup is out of scope of this document. Once you have ssl setup for your OS, access the web page using https:// instead of http://
Also add the SSLRequireSSL directive for the cgi-bin Directory section in httpd.conf. This would force ssl access every time you access the web interface.
For example
<Directory "/usr/local/www/apache22/cgi-bin"> AllowOverride AuthConfig Limit SSLRequireSSL Options None Order allow,deny Allow from all </Directory>
